Supplier Identity Access Management: Why External Identities Need the Same Governance as Employees
Supplier identity access management is one of the most consistently overlooked areas of identity governance in manufacturing environments.
Internal workforce identities get lifecycle automation, role-based provisioning, and regular access certification. External supplier identities often get a manually created account, an email with credentials, and very little after that.
The gap between those two experiences is where risk accumulates.
The Problem With How Supplier Access Is Typically Managed
In most manufacturing organizations, supplier and partner identities are managed outside the core IGA platform. Accounts are created manually — often by request via email or a service desk ticket. Roles are assigned inconsistently. And when the supplier project ends, or the personnel change, deprovisioning rarely happens automatically.
The practical consequences are straightforward:
Dormant accounts persist. A supplier engineer finishes a project and moves on. Their account remains active in the SAP portal, the quality management system, or the engineering collaboration environment. Nobody flags it because nobody is tracking it.
Privilege accumulates over time. Supplier users gain access to additional systems as projects evolve. When scopes change or contracts end, that access is rarely walked back to match the new reality.
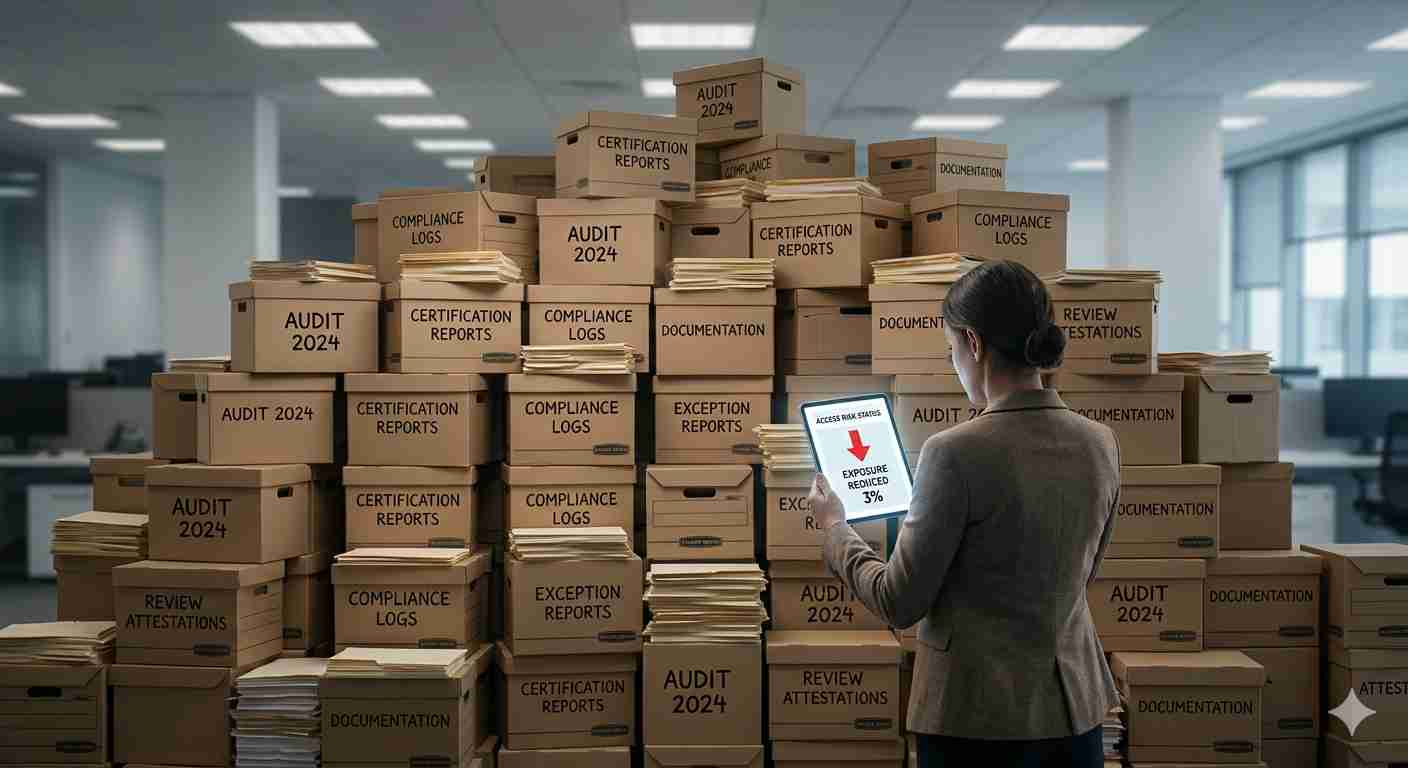
There is no audit trail. When an auditor or incident responder asks who had access to a specific system and when, the answer for external identities is often incomplete or unavailable.
These are not edge cases. They are the default state of supplier identity access management in organizations that have not extended their IGA framework to external participants.
What External Identity Lifecycle Management Actually Requires
Fixing supplier identity access management is not primarily a tooling problem. It is a process and governance problem — and it starts with applying the same lifecycle discipline to external identities that already exists for employees.
That means four things in practice:
1. Structured onboarding with defined roles. Supplier access should be provisioned through the same request and approval workflow used for employees — with a defined business justification, a role assignment based on actual need, and a named internal owner accountable for the relationship.
2. Time-bound access by default. Unlike employees, supplier relationships have a defined scope and duration. Access should reflect that. Time-bound provisioning — with automatic expiry tied to contract or project end dates — closes the dormant account problem without requiring manual follow-up.
3. Continuous monitoring and periodic review. Supplier access should be included in regular access certification campaigns. Usage data — last login, activity frequency, systems accessed — should be surfaced at the point of review so certifiers can make informed decisions rather than defaulting to approval.
4. Automated deprovisioning on relationship change. When a supplier contract ends, when a supplier employee leaves a project, or when an engagement scope changes, access revocation should trigger automatically — not depend on a manual request from a procurement or vendor management team that may not have a direct line to IT.
IGA Supplier Access: Extending the Governance Framework
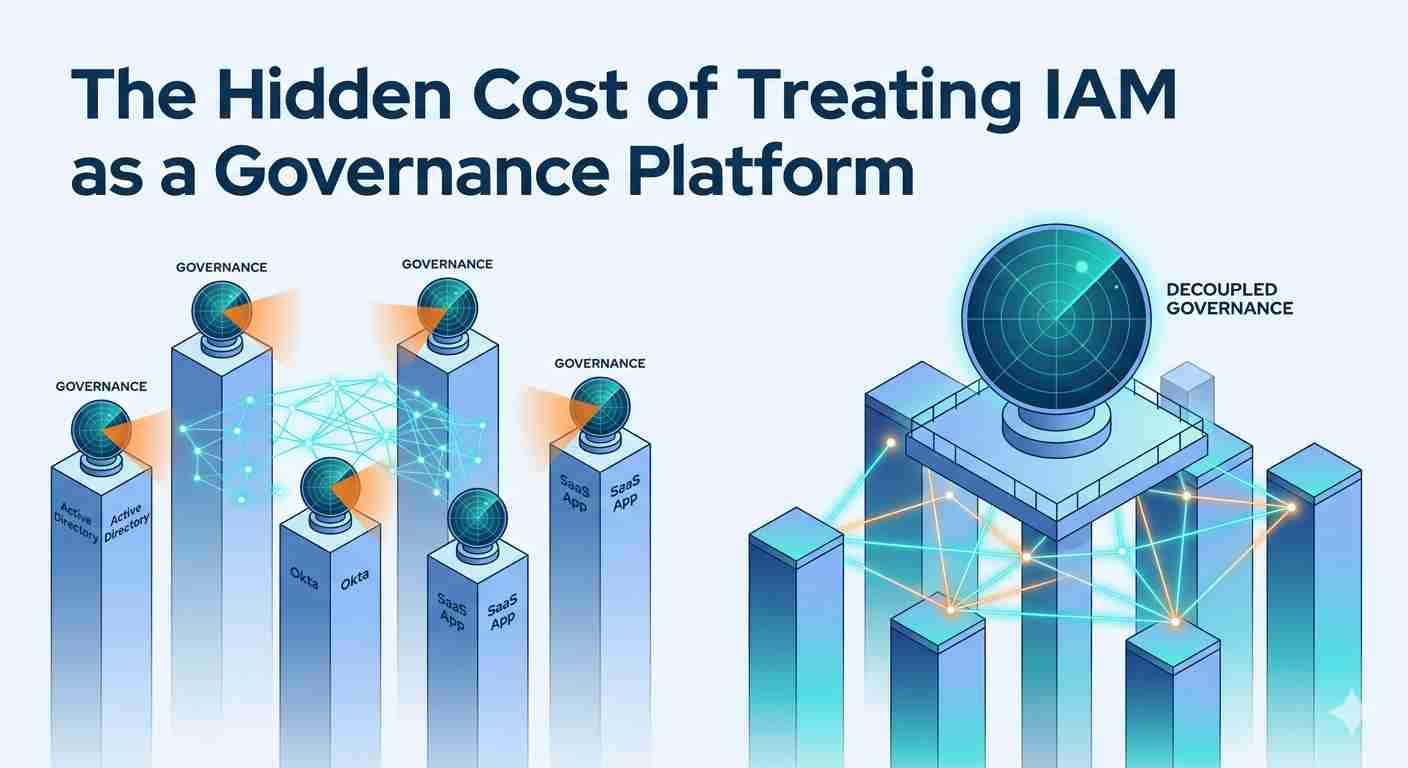
For IT and security teams, the practical challenge is extending IGA supplier access controls to external identities without creating a parallel governance system.
The most effective approach is to bring supplier identities into the same IGA platform used for workforce governance — using the same provisioning workflows, the same role model, and the same certification process. External identities are treated as a distinct population within a unified framework, rather than a separate problem managed through spreadsheets and service tickets.
This requires two things the IGA platform needs to support:
External identity onboarding — the ability to create and manage identities for users who are not in the corporate HR system, with appropriate workflows for invitation, approval, and lifecycle tracking
Integration with supplier-facing systems — the SAP portals, PLM environments, MES platforms, and supply chain systems that supplier users actually access
When these capabilities are in place, supplier identity access management becomes a governed, auditable process — not an afterthought.
Partner Access Governance in Manufacturing: The Broader Picture
Suppliers are one population. Partners, contractors, logistics providers, and service firms are others. Each has different access requirements and different lifecycle patterns — but all benefit from the same governance principles.
Partner access governance in manufacturing means applying consistent policy across all external participants: structured provisioning, time-bound access, regular review, and automated deprovisioning. The specifics vary by population. The framework does not.
Conclusion: External Identities Deserve First-Class Governance
Supplier and partner identities interact with some of the most sensitive systems in manufacturing environments — ERP platforms, product lifecycle systems, quality management tools, and supply chain portals.
They deserve the same governance discipline as internal workforce identities. Not a manual workaround. Not a spreadsheet. A structured, automated, auditable process — built into the same identity framework that governs everyone else.
For a broader look at how identity governance applies across workforce, supplier, and partner ecosystems in manufacturing, see: Identity in Industrial Ecosystems: Securing Workforce, Suppliers, and Partners.
Know More at: https://www.openiam.com/blog/i....dentity-in-industria